Blockchain-enabled Wireless Internet of Things: Network Architecture and Performance Analysis
Yao Sun, National Key Lab on Communications, University of Electronic Science and Technology of China, China; Bin Cao, State Key Laboratory of Networking and Switching Technology, Beijing University of Posts and Telecommunications, China; Lei Zhang, James Watt School of Engineering, University of Glasgow, UK; and Muhammad Ali Imran, James Watt School of Engineering, University of Glasgow, UK
IEEE Blockchain Technical Briefs, September 2019
Discuss this topic on IEEE Collabratec
I. Introduction and Background
IoT is envisioned as one of the most promising technologies for constructing a global network with machines and devices which will gradually cover almost all aspects of the human life [1], [2]. With such an important role it plays in our life, there is a consensus that the security problem is of the first priority of IoT [3], [4] due to the easy accessibility and hardware/software constraints on IoT devices. Moreover, in the current centralized IoT system, due to the involvement of the third party, the high agent cost makes smart contract [5] (such as micro payment and information exchange) among devices unattractive, and thus poses a bottleneck on the prosperous of IoT ecosystems.
As a revolution in systems of record, blockchain has been regarded as a promising technology to address IoT’s trust and security concerns, as well as high maintenance cost problem [5], [6]. The blockchain is formed by a continuously growing set of data blocks, and each data block is generated by processing the transaction information with certain cryptography algorithms. The main principles underlying the blockchain are summarized as follows [7], [8]:
- The transactions happen directly between peers instead of through a central server, and each transaction information will be forwarded to all other nodes.
- Each node within the blockchain has the right to access to the entire database, and contributes to the calculation and verification of the new block generated by the collected transactions.
- Various cryptography algorithms and consensus mechanisms are implemented to guarantee the records in the database. It is extremely difficult for any single party to tamper or delete the records as they are correlated to every transaction record before them.
- The system is secure as long as a certain percentage of CPU power (for example 51% in PoW system) within the system is not controlled by any cooperating group of attacker nodes.
Because of the above features, blockchain technique could enable cost effective and highly safe transaction, which is exactly the missing part of the current IoT ecosystems. Specifically, blockchain allows the secured and reliable transactions between two smart devices without the need of centralized authority, which improves the settlement time from days to almost instantaneous apart from saving the additional costs incurred by the centralized third party.
II. Motivations
There are some problems associated with the combination of blockchain and IoT. As pointed by [5], it is computationally intensive and power consuming to implement the current blockchain technique (especially PoW based one), but most of the IoT devices may not have enough computing capability, memory space as well as power supplement to run and store blockchain. Relevant state-of-the-art work focuses on the blockchain protocols design in terms of consensus mechanism, trust and privacy, etc. while no more consideration on an efficient network architecture to support low cost blockchain-enabled wireless IoT system [9], [10]. Only the authors in work [11] propose a blockchain-enabled IoT network architecture with requirement of central management which is more suitable for a small local network (such as smart home).
From the communication perspective, in the traditional blockchain systems, a common assumption is that communications among the nodes are perfect without delay constraints. However, considering the unstable channel quality, interference, limited resource and various network topology, it is necessary to investigate the impact of wireless communication on the blockchain-enabled IoT system. In general, the performance of blockchain-enabled IoT system in terms of transaction throughput (the number of confirmed transactions in a unit time), communication throughput (the amount of transmitted data in a unit time), transaction successful rate should be associated with both blockchain transaction arrival rate in time domain and nodes geographic distribution in spatial domain. Therefore, a fundamental challenge is that how to establish a valid framework of analytical model considering the two-dimensional randomness to evaluate the performance of blockchain-enabled IoT system.
Although there has been tremendous research work on wireless network modeling, the existing performance analysis focusing on wireless networks cannot be directly applied to blockchain-enabled IoT system due to the lack consideration of blockchains. In addition to communication performance analysis for block-enabled IoT system, security performance analysis is also necessary when some attacks exist in this system. Considering the vulnerable wireless links, the types of attacks could be various. To the best of the authors' knowledge, there is no such analytical models dedicated to blockchain-enabled wireless IoT systems.
III. Technical Skeleton
In this paper, we first present a new network model for blockchain-enabled IoT system. Then we theoretically analyze the performance of the blockchain-enabled IoT system, and propose an optimal blockchain full function node (i.e., full function node has high computing and storage power with full functionalities to support blockchain protocols) deployment based on the analysis. Finally, we analyze the security performance in the proposed system. Therefore, the technical skeleton of this work can be summarized as follows.
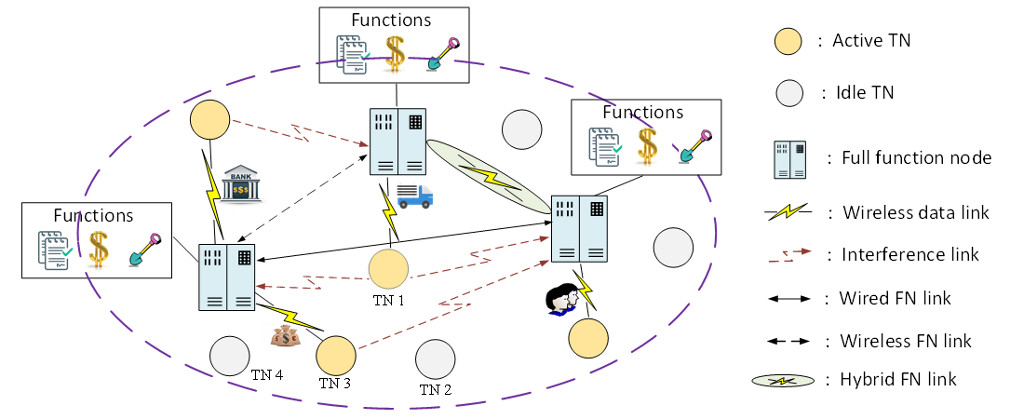
Figure 1. Blockchain-enabled wireless IoT system model
1) Blockchain-enabled Wireless IoT System Model
The blockchain-enabled IoT network model is shown in Fig. 1, which consists of three main elements: full function nodes (FNs), IoT transaction nodes (TNs) and the transactions. Any valuable information transmission between TNs can be considered as transactions.
TNs are typically composed of low-end IoT devices. At any time point, each TN's status is either active (with data transmissions) or idle (with no data transmission). FNs are normally the authorized nodes with high computing and storage abilities. They have full functionalities with respect to blockchain protocols thus bear the responsibility for transaction confirmation, data storage and building new blocks. Once a new transaction arrives, the TN will broadcast the information to the whole network for verification, after which the FN who has the right of building a block will insert this transaction into the chain, and all FNs need to update their own database accordingly.
2) Performance Analysis of the Proposed System
We theoretically analyze the performance of the proposed blockchain-enabled IoT system. In detail, considering the spatio-temporal domain Poisson point process (PPP) modeling, i.e., node geographical distribution and transaction arrival rate in time domain, we derive the probability density function (PDF) of SINR for a transmission from an IoT node to a full function node. Accordingly, the transaction successful rate and overall communication throughput are calculated.
3) Optimal Full Function Node Deployment
Based on the derived analytical model, a searching algorithm can be designed to find the optimal blockchain full function node deployment under a given IoT node’s density and blockchain transaction throughput.
4) Security Performance Analysis
The security performance is analyzed in the proposed system with three typical kinds of attacks, i.e., eclipse attack, random link attack and random node attack. Solutions such as physical layer security could be presented and discussed to keep the system secure under such attacks. Specifically, PHY-layer authentication techniques exploit the spatial decorrelation property of the PHY-layer information, such as received signal strength indicators, received signal strength, channel phase response, channel impulse responses, and channel state information to distinguish radio transmitters, and thus detect spoofing attacks with low overhead.
IV. Conclusions
In this work, we first propose a blockchain-enabled wireless IoT system model and then present fundamental analysis framework to underpin the blockchain enabled IoT system. The framework of the system model and analysis approach establish a foundation for further complex blockchain enabled system performance analysis and protocol design.
References
[1] I. LEE and K. Lee, “The Internet of Things (IoT): Applications, invest- ments, and challenges for enterprises,” Business Horizons, vol. 58, no. 4, pp. 431–440, 2015.
[2] A. Bassi and G. Horn, “Internet of Things in 2020: A Roadmap for the Future,” European Commission: Information Society and Media, pp. 97–114, 2008.
[3] M. . Farooq, M. Waseem, A. Khairi, et al., “A Critical Anal- ysis on the Security Concerns of Internet of Things (IoT),” International Journal of Computer Applications, vol. 111, no. 7, 2015.
[4] T. Xu, J. B. Wendt, and M. Potkonjak, “Security of IoT Systems: Design Challenges and Opportunities,” in 2014 IEEE/ACM International Conference on Computer-Aided Design, 2014, pp. 417–423.
[5] K. Christidis and M. Devetsikiotis, “Blockchains and Smart Contracts for the Internet of Things,” IEEE Access, pp. 2292–2303, 2016.
[6] Z. Zheng, S. Xie, H.-N. Dai, et al., “Blockchain Challenges and Opportunities: A Survey,” International Journal of Web and Grid Services, vol. 14, no. 4, pp. 352–375, 2016.
[7] M. Iansiti and K. R. Lakhani, “The Truth about Blockchain,” Harvard Business Review, vol. 95, no. 1, pp. 118–127, 2017.
[8] S. Nakamoto, “Bitcoin: A peer-to-peer Electronic Cash System,” [Online]. Available: https://bitcoin.org/bitcoin.pdf, 2008.
[9] O. Choudhury, H. Sarker, N. Rudolph, et al., “Enforcing human subject regulations using blockchain and smart contracts,” Blockchain in Healthcare Today, 2018.
[10] P. Genestier, S. Zouarhi, P. Limeux, et al., “Blockchain for consent management in the ehealth environment: A nugget for privacy and security challenges.,” Journal of the International Society for Telemedicine and eHealth, 2017.
[11] A. Dorri, S. S. Kanhere, R. Jurdak, et al., “Blockchain for IoT security and privacy: The case study of a smart home,” in 2017 IEEE International Conference on Pervasive Computing and Communications Workshops (PerCom Workshops), 2017, no. January, pp. 618–623.
 Yao Sun received the Ph.D. degree in Communication Engineering from the University of Electronic Science and Technology of China (UESTC). He is currently a research fellow at UESTC. His research interests include blockchain system, internet of things and resource management in mobile networks.
Yao Sun received the Ph.D. degree in Communication Engineering from the University of Electronic Science and Technology of China (UESTC). He is currently a research fellow at UESTC. His research interests include blockchain system, internet of things and resource management in mobile networks.
 Bin Cao is an associate researcher in the State Key Laboratory of Networking and Switching Technology at Beijing University of Posts and Telecommunications. He was a research fellow at the National University of Singapore from July 2015 to July 2016. He served as symposium cochair for IEEE ICNC 2018, workshop cochair for CyberC 2019 and TPC member for numerous conferences. His research interests include blockchain system, internet of things and mobile edge computing.
Bin Cao is an associate researcher in the State Key Laboratory of Networking and Switching Technology at Beijing University of Posts and Telecommunications. He was a research fellow at the National University of Singapore from July 2015 to July 2016. He served as symposium cochair for IEEE ICNC 2018, workshop cochair for CyberC 2019 and TPC member for numerous conferences. His research interests include blockchain system, internet of things and mobile edge computing.
 Lei Zhang (SM'18) is now a Lecturer at the University of Glasgow, UK. His research interests broadly lie in the Communications and Array Signal Processing. Dr Lei Zhang also holds a visiting position in 5GIC at the University of Surrey. He is an associate editor of IEEE ACCESS and a senior member of IEEE.
Lei Zhang (SM'18) is now a Lecturer at the University of Glasgow, UK. His research interests broadly lie in the Communications and Array Signal Processing. Dr Lei Zhang also holds a visiting position in 5GIC at the University of Surrey. He is an associate editor of IEEE ACCESS and a senior member of IEEE.
 Muhammad Ali Imran (M'03, SM'12) is a Professor of Wireless Communication Systems with research interests in self organized networks, wireless networked control systems and the wireless sensor systems. He heads the Communications, Sensing and Imaging CSI research group at University of Glasgow. He is an Affiliate Professor at the University of Oklahoma, USA and a visiting Professor at 5G Innovation Centre, University of Surrey, UK.
Muhammad Ali Imran (M'03, SM'12) is a Professor of Wireless Communication Systems with research interests in self organized networks, wireless networked control systems and the wireless sensor systems. He heads the Communications, Sensing and Imaging CSI research group at University of Glasgow. He is an Affiliate Professor at the University of Oklahoma, USA and a visiting Professor at 5G Innovation Centre, University of Surrey, UK.
Editor:
 Honggang Wang was the "Scholar of The Year" (2016). Before he joined UMass Dartmouth in 2009, he has worked for Bell Labs Lucent Technologies China from 2001 to 2004 as a Member of Technical Staff. He received his Ph.D. in Computer Engineering at University of Nebraska-Lincoln in 2009. He is a tenured associate professor at UMass Dartmouth. His research interests include Internet of Things, Wireless Health, Body Area Networks (BAN), Cyber and Multimedia Security, Mobile Multimedia and Cloud, Wireless Networks and Cyber-physical System, and BIG DATA in mHealth. He has published more than 150 papers in his research areas. He was an invited participant by National Academic Engineering (NAE) for 2017 German-American Frontiers of Engineering Symposium, as one of about 50 outstanding engineers (ages 30-45) from US companies, universities, and government labs. He has served as the general chair/co-chair and TPC chair/co-chairs for many IEEE conferences. He also serves as the steering committee co-chair of IEEE CHASE and TPC co-chair of IEEE CHASE 2016, which is a leading international conference in the field of connected health. He has also been serving as the Associate Editor in Chief (EiC) for IEEE Internet of Things journal (SCI impact factor: 7.596), associate editors for IEEE Transactions on Big Data and IEEE Transactions on Multimedia, an Editor of IEEE Transactions on Vehicular Technology, Associate Technical Editor of IEEE Communication Magazine. He received IEEE Multimedia Communications Technical Committee (MMTC) Outstanding Leadership Award (2015) and IEEE HEALTHCOM 2015 Outstanding Service Award. His research is supported by NSF DoT, UMass President office, and UMass Healey Grant (total over 2M dollars).
Honggang Wang was the "Scholar of The Year" (2016). Before he joined UMass Dartmouth in 2009, he has worked for Bell Labs Lucent Technologies China from 2001 to 2004 as a Member of Technical Staff. He received his Ph.D. in Computer Engineering at University of Nebraska-Lincoln in 2009. He is a tenured associate professor at UMass Dartmouth. His research interests include Internet of Things, Wireless Health, Body Area Networks (BAN), Cyber and Multimedia Security, Mobile Multimedia and Cloud, Wireless Networks and Cyber-physical System, and BIG DATA in mHealth. He has published more than 150 papers in his research areas. He was an invited participant by National Academic Engineering (NAE) for 2017 German-American Frontiers of Engineering Symposium, as one of about 50 outstanding engineers (ages 30-45) from US companies, universities, and government labs. He has served as the general chair/co-chair and TPC chair/co-chairs for many IEEE conferences. He also serves as the steering committee co-chair of IEEE CHASE and TPC co-chair of IEEE CHASE 2016, which is a leading international conference in the field of connected health. He has also been serving as the Associate Editor in Chief (EiC) for IEEE Internet of Things journal (SCI impact factor: 7.596), associate editors for IEEE Transactions on Big Data and IEEE Transactions on Multimedia, an Editor of IEEE Transactions on Vehicular Technology, Associate Technical Editor of IEEE Communication Magazine. He received IEEE Multimedia Communications Technical Committee (MMTC) Outstanding Leadership Award (2015) and IEEE HEALTHCOM 2015 Outstanding Service Award. His research is supported by NSF DoT, UMass President office, and UMass Healey Grant (total over 2M dollars).
Subscribe to the IEEE Blockchain Technical Briefs
Join our Blockchain Technical Community and receive our Technical Briefs by email.
IEEE Blockchain Technical Briefs Editorial Board
Gora Datta, FHL7, SMIEEE, SMACM, Managing Editor
2024 Editorial Team
Justin Y. Shi, PhD, Editor-in-Chief
Boleslaw K. Szymanski, PhD
R.L. Shankar, PhD
Imran Bashir
Nicolae "Nicu" Goga, PhD
Constantin “Viorel” Marian, PhD
View the 2023 IEEE Blockchain Technical Briefs Editorial Board
View the 2022 IEEE Blockchain Technical Briefs Editorial Board
View the 2018-2020 IEEE Blockchain Technical Briefs Editorial Board
Past Issues
Read the top five most popular IEEE Blockchain Technical Briefs articles.
Read more (PDF, 731 KB)