Trust Evaluation Based on Blockchain in Pervasive Social Networking
Zheng Yan* and Li Peng1, Xidian University, China
IEEE Blockchain Technical Briefs, September 2018
In recent years, heterogeneous networks organized by the Internet, mobile cellular networks and self-organized Mobile Ad hoc Networks (MANETs) have received special attention due to their capabilities of establishing an instant communication platform for time-critical or mission-critical applications. As a concrete application example, Pervasive Social Networking (PSN) supports instant social activities anywhere and at any time in an intelligent and context-aware manner by switching among heterogeneous networks based on user demands [1].
Without any doubt, trust plays a crucial role in PSN since it assists decision making in social activities [2]. But building up a real trust relationship and evaluating trust in a decentralized way are still not an easy task, especially among people located in different places without any face to face interactions and pre-established trust relationships. This issue becomes more serious and critical in PSN [3]. Such a social network, different from online social networking, generally lacks a centralized party to help information collection, social data aggregation and trust/reputation generation [4]. A number of issues should be addressed in terms of trust evaluation, as described below:
Decentralization. First, the literature lacks real decentralized trust evaluation in social networking. Many existing works on trust evaluation in social networking normally depend on a trusted third party to collect social communication data and social networking behavior data to perform information fusion and aggregation in order to conduct trust evaluation or reputation generation [8]. Trust evaluation at a specific PSN node based on locally collected but incomplete information is normally not accurate, with bias. Reputation generation needs to rely on a single node or party. Thus, trust authentication has to depend on a centralized party [3]. In short, past solutions about trust evaluation and trust authentication are centralized. But this kind of solutions cannot exactly fit into PSN, which is actually a distributed system. An effective and purely decentralized trust evaluation and authentication scheme is highly needed.
Trustworthiness. The literature requests that trust evaluation should be trustworthy. We hope trust evaluation is transparent, open, traceable and non-repudiable, and thus the trustworthiness of trust evaluation can be ensured. However, some existing distributed trust evaluation solutions cannot achieve this goal since we cannot verify if the trust evaluation is rational, without any defect. Therefore, it is hard to ensure aggregated trust or reputation based on local trust is creditable. How to support public auditing on trust evaluation is still an open issue.
Lightweight and Efficiency. Although blockchain technology provides a great advantage to realize decentralized management, some blockchain-based distributed applications have low efficiency. They consume a lot of resources due to high computation cost caused by consensus mechanisms, such as Proof-of-Work [9, 10], which is hard to be applied in resource-constrained mobile devices in PSN. If blockchain is to be used for trust evaluation, a lightweight and efficient solution is critical for PSN distributed applications.
Blockchain has become a hot technique since the appearance of Bitcoin in 2008 [5]. Recently, it has drawn wide attention in both academia and industry due to its advantage of supporting decentralized functionalities in a transparent and immutable way. Inspired by its application in Bitcoin, blockchain has been extensively researched for providing decentralized security solutions in the areas of cryptocurrencies, Internet of Things, cloud computing, data management, healthcare services, shared economy, etc. However, applications based on blockchain are still in their infancy. The consensus mechanisms, such as Proof-of-Work (PoW), Proof-of-Stake (PoS), Delegated Proof of Stake (DPOS), Practical Byzantine Fault Tolerance (PBFT), and Directed Acyclic Graph (DAG) [6], adopted in Bitcoin and other blockchain-based systems generally cost a lot of computational resources and/or may not ensure consistency on block generation. They are not immediately ready for trust evaluation in PSN though blockchain is a promising technique to achieve trust management in the context of PSN [7].
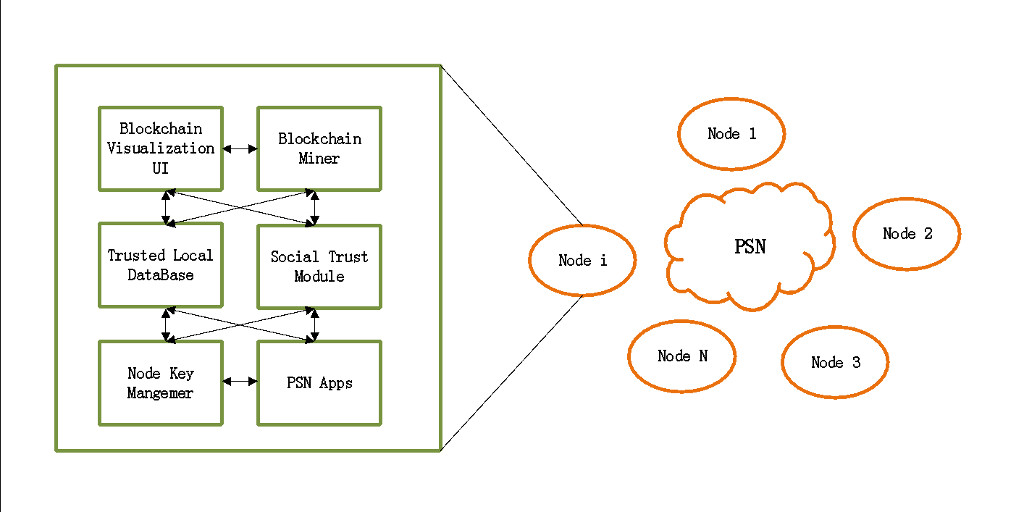
To solve existing open issues in trust evaluation in PSN, we propose a novel blockchain-based solution, including a trust evaluation algorithm, a novel consensus mechanism. a new incentive mechanism, a mining winner selection algorithm and a consensus policy setting algorithm. The structure of our system is shown in Figure 1. We briefly introduce the core designs of our solution as below.
Figure 1: System Structure.
- The system contains a number of nodes that make use of heterogeneous networks for pervasive social networking. Some nodes also behave as miners to maintain the blockchain that is used for trust evaluation and authentication in a decentralized manner. Any node can behave as a miner, namely mining node. Each node contains a number of basic functional modules. Some PSN apps are used to perform different kinds of social networking for different social purposes. Blockchain Visualization UI is applied to display the contents of blockchain. Blockchain Manager is responsible for performing the tasks that should be done by a mining node if the underlying node wants to be a miner. Node Key Manager is responsible for generating a personal key pair, hashing data, checking data integrity and signing/verifying signatures. Social Trust Module is designed to record social networking data statistics, handle communications between the node and miners and report local trust and trust evidence to the miners. All information related to the above functional modules is stored at Trusted Local DataBase, e.g., latest blockchain if need to keep a copy locally, local records about social networking, public-private key pairs, etc.
- For trust evaluation, we propose that every time a PSN node communicates with other nodes, trust evidence will be produced and be broadcasted in the PSN network, a number of mining nodes (i.e., miners) perform trust evaluation by verifying and aggregating sufficient evidence collected after previous block is generated in order to calculate the trust values of related nodes based on a pre-agreed common algorithm.
- We use blockchain to support trust evaluation and manage the whole PSN system. Regarding the consensus mechanism applied for block generation, the miner that generates a new block announces it in PSN to other miners. The next block will be generated if its mining work can be approved by other miners when the sum of mining nodes' trust values is above a threshold and the total number of approving miners is above an expected number. The trust value threshold and the miner number threshold are decided by the consensus policy setting algorithm. The pre-agreed trust evaluation algorithm should be executed by all miners for block mining verification. This is a kind of Proof-of-Trust consensus mechanism. The design holds the principle that the sufficient number of reputable miners decide the correctness of the blockchain. Notably, the function applied for trust evaluation has low computation complexity in our design, thus it is feasible to be operated in mobile devices.
- We propose that the mining winner is awarded a token, which should be signed by all the miners who approved a new block. The token can be used for specific social activities (e.g., advertisement) or gaining some benefits (e.g., coupons). This incentive mechanism can attract miners to work actively.
- To make sure that there is only one winner recognized by mining nodes at the same time, we take the block generation time, the number of tokens owned by a node and some other factors into consideration to design the mining winner selection algorithm in order to avoid blockchain fork as much as possible.
The proposed blockchain-based trust evaluation in PSN can solve the open issues of distributed trust evaluation, as summarized before. We are currently implementing and evaluating our solution to verify its performance in terms of decentralization, trustworthiness, lightweight and efficiency, as well as trust evaluation robustness. Future work includes access control based on trust, privacy-preserving trust evaluation, and so forth.
* Zheng Yan is with the Key Lab of Information Network Security, Ministry of Public Security, China, the State Key Laboratory of ISN, School of Cyber Engineering, Xidian University, Xi'an, China and the Department of Communications and Networking, Aalto University, Finland (email: zyan@xidian.edu.cn)
1 Li Peng is with the State Key Laboratory of ISN, School of Cyber Engineering, Xidian University, Xi'an, China (email: pengli_email@163.com)
Acknowledgement
1) The work is supported in part by the National Natural Science Foundation of China under Grant 61672410, and Grant U1536202.
2) The work is supported in part by the Academy of Finland under Grant 308087.
3) The work is supported in part by the Project Supported by Natural Science Basic Research Plan in Shaanxi Province of China under grant No. 2016ZDJC-06.
4) The work is supported in part by the Key Lab of Information Network Security, Ministry of Public Security under grant No. C18614.
5) The work is supported in part by the National Key Research and Development Program of China under Grant 2016YFB0800700.
6) The work is supported in part by the 111 project under grant B08038 and grant B16037.
References
[1] Z. Yan and M.J. Wang. “Protect pervasive social networking based on two-dimensional trust levels,” IEEE Systems Journal, vol. 11, no. 1, pp.207-218, 2017.
[2] Z. Yan, H.G. Wang, L.T. Yang, and V. Niemi, “Editorial on special session on trust management in pervasive social networking (TruPSN),” IEEE Access, vol. 6, no. 1, pp. 16851-16854, Dec. 2018.
[3] Z. Yan, W. Feng, and P. Wang, “Anonymous authentication for trustworthy pervasive social networking,” IEEE Transactions on Computational Social Systems, vol. 2, no. 3, pp. 88-98, Feb. 2016.
[4] Z. Yan, P. Wang, and W. Feng, “A novel scheme of anonymous authentication on trust in pervasive social networking,” Information Sciences, 2018. Doi: 10.1016/j.ins.2018.02.037
[5] S. Nakamoto, “Bitcoin: A peer-to-peer electronic cash system,” 2008. Retrieved from https://bitcoin.org/bitcoin.pdf
[6] C. Gong, “5 Types of Blockchain Consensus Mechanisms,” April 16, 2018. Retrieved from https://www.logicsolutions.com/5-types-blockchain-consensus-mechanisms/
[7] A. Singh, “What is the major limitation of blockchain technology?” January 3, 2018. Retrieved from https://www.quora.com/What-is-the-major-limitation-of-blockchain-technology
[8] Z. Yan, Y. Chen, and Y. Shen, “A practical reputation system for pervasive social chatting,” Journal of Computer and System Sciences, vol. 79, issue 5, pp.556-572, 2013.
[9] R. Dennis and G. Owen. “Rep on the block: a next generation reputation system based on the blockchain,” 10th IEEE International Conference for Internet Technology and Secured Transactions (ICITST), 2016.
[10] T. McConaghy, et al. “BigchainDB: a scalable blockchain database,” white paper, BigChainDB, 2016.
 Zheng Yan is currently a full professor at the Xidian University, China and a visiting professor and Finnish academy research fellow at the Aalto University, Finland. She received the Doctor of Science in Technology from the Helsinki University of Technology, Finland. She authored and co-authored about 200 peer-reviewed articles, 8 conference proceedings and solely authored two books. She is an inventor of 60+ granted patents and PCT patents, all of them were adopted or purchased by industry. Some of her granted patents are applied in international standards. She has given 20 keynotes and invited talks in international conferences and universities. Her research interests are in trust, security and privacy; data mining; mobile applications and services; social networking and cloud computing. Prof. Yan serves as an organizational and technical committee member for more than 80 international conferences and workshops. She is an associate editor of IEEE IoT Journal, Information Fusion, Information Sciences, IEEE Access, JNCA, Soft Computing, IEEE Blockchain Technical Briefs, Security and Communication Networks, etc. and a special issue leading guest editor of ACM TOMM, Future Generation Computer Systems, Computers & Security, IJCS, MONET, IEEE Systems Journal, etc. She is a founder steering committee co-chair of IEEE Blockchain conference. She is organizing and has organized 10+ conferences, such as IEEE Blockchain 2018, NSS/ICA3PP/IEEE CIT2017, IEEE TrustCom/BigDataSE/ISPA-2015, IEEE CIT2014, etc. Her recent awards include a number of Outstanding Leadership Awards for IEEE conference organization; the 2017 IEEE ComSoc TCBD Best Journal Paper Award; Outstanding Associate Editor of 2017 for IEEE Access; EU Eureka Excellence Award (2017); Best Individual of Shaanxi Province from Abroad (2014), “100 Expert Plan” winner of Shaanxi Province, China (2011); Sisu Award of Nokia Research Center (2010); EU ITEA Bronze Achievement Award (2008). She is a senior member of IEEE.
Zheng Yan is currently a full professor at the Xidian University, China and a visiting professor and Finnish academy research fellow at the Aalto University, Finland. She received the Doctor of Science in Technology from the Helsinki University of Technology, Finland. She authored and co-authored about 200 peer-reviewed articles, 8 conference proceedings and solely authored two books. She is an inventor of 60+ granted patents and PCT patents, all of them were adopted or purchased by industry. Some of her granted patents are applied in international standards. She has given 20 keynotes and invited talks in international conferences and universities. Her research interests are in trust, security and privacy; data mining; mobile applications and services; social networking and cloud computing. Prof. Yan serves as an organizational and technical committee member for more than 80 international conferences and workshops. She is an associate editor of IEEE IoT Journal, Information Fusion, Information Sciences, IEEE Access, JNCA, Soft Computing, IEEE Blockchain Technical Briefs, Security and Communication Networks, etc. and a special issue leading guest editor of ACM TOMM, Future Generation Computer Systems, Computers & Security, IJCS, MONET, IEEE Systems Journal, etc. She is a founder steering committee co-chair of IEEE Blockchain conference. She is organizing and has organized 10+ conferences, such as IEEE Blockchain 2018, NSS/ICA3PP/IEEE CIT2017, IEEE TrustCom/BigDataSE/ISPA-2015, IEEE CIT2014, etc. Her recent awards include a number of Outstanding Leadership Awards for IEEE conference organization; the 2017 IEEE ComSoc TCBD Best Journal Paper Award; Outstanding Associate Editor of 2017 for IEEE Access; EU Eureka Excellence Award (2017); Best Individual of Shaanxi Province from Abroad (2014), “100 Expert Plan” winner of Shaanxi Province, China (2011); Sisu Award of Nokia Research Center (2010); EU ITEA Bronze Achievement Award (2008). She is a senior member of IEEE.
 Li Peng received his Bachelor’s degree from the School of Cyber Engineering, Xidian University in 2018 and he is currently pursuing his Ph.D. degree. His main research interests include blockchain and its application, as well as, social communication security.
Li Peng received his Bachelor’s degree from the School of Cyber Engineering, Xidian University in 2018 and he is currently pursuing his Ph.D. degree. His main research interests include blockchain and its application, as well as, social communication security.
Editor:
 Dr. Shucheng Yu is an Associate Professor of Electrical and Computer Engineering at Stevens Institute of Technology. Before he joined Stevens, Dr. Yu was an associate professor of Computer Science at the University of Arkansas at Little Rock, where he also served as the chair of the Computer Science department and the director of the Computational Research Center of the university. He received his PhD in Electrical and Computer Engineering from Worcester Polytechnic Institute in 2010. His research interest is on cybersecurity in general, with recent focuses on security and privacy for data analytics, security & privacy in smart systems, wireless systems and security. He has published over sixty impactful research articles in academic journals and conference proceedings which have received numerous citations. He has been the editor or guest editor for four international journals, and at the organizing committee for over ten international conferences including IEEE Infocom and IEEE Globecom. He serves the board of trustee for Wireless and Optical Communication Conference (WOCC) and is a member of IEEE and ACM.
Dr. Shucheng Yu is an Associate Professor of Electrical and Computer Engineering at Stevens Institute of Technology. Before he joined Stevens, Dr. Yu was an associate professor of Computer Science at the University of Arkansas at Little Rock, where he also served as the chair of the Computer Science department and the director of the Computational Research Center of the university. He received his PhD in Electrical and Computer Engineering from Worcester Polytechnic Institute in 2010. His research interest is on cybersecurity in general, with recent focuses on security and privacy for data analytics, security & privacy in smart systems, wireless systems and security. He has published over sixty impactful research articles in academic journals and conference proceedings which have received numerous citations. He has been the editor or guest editor for four international journals, and at the organizing committee for over ten international conferences including IEEE Infocom and IEEE Globecom. He serves the board of trustee for Wireless and Optical Communication Conference (WOCC) and is a member of IEEE and ACM.
Subscribe to the IEEE Blockchain Technical Briefs
Join our Blockchain Technical Community and receive our Technical Briefs by email.
IEEE Blockchain Technical Briefs Editorial Board
Gora Datta, FHL7, SMIEEE, SMACM, Managing Editor
2024 Editorial Team
Justin Y. Shi, PhD, Editor-in-Chief
Boleslaw K. Szymanski, PhD
R.L. Shankar, PhD
Imran Bashir
Nicolae "Nicu" Goga, PhD
Constantin “Viorel” Marian, PhD
View the 2023 IEEE Blockchain Technical Briefs Editorial Board
View the 2022 IEEE Blockchain Technical Briefs Editorial Board
View the 2018-2020 IEEE Blockchain Technical Briefs Editorial Board
Past Issues
Read the top five most popular IEEE Blockchain Technical Briefs articles.
Read more (PDF, 731 KB)